What are the Advantages of Buying THC Vape From Online Vendors?
If you are thinking about purchasing a THC vape, then it’s worth considering the numerous advantages of buying online. As…
RAID Controller
RAID controller Is a storage component that will store and manage the disk drives in a RAID infrastructure. It stands…
Web3 And Metaverse: The Next Frontier Of Internet
Web3 And Metaverse – The development of metaverse technology in this century has sparked a number of revolutionary ideas that…
AI-Powered Adventures: Enhancing Your Trip with Smart Technology
Travel has always been an adventure, a journey filled with discoveries and moments that linger in memory. Yet, in today’s…
Advanced Host Controller Interface
Advanced host controller interface is defined as a technical standard by Intel that will mainly work on the registered level…
Identity Provider
Identity provider is the process that will create a commerce store and manage digital identities. The IDP will provide authentication…
Team Collaboration
Team collaboration is working together on a project or presentation to achieve a better result that would be difficult to…
Radio Access Network
The radio access network is part of the mobile network connecting end-user devices, such as mobile phones, to the cloud….
Value Chain
A value chain is the consecutive steps from creating a final product to delivering it to customers. This chain will…
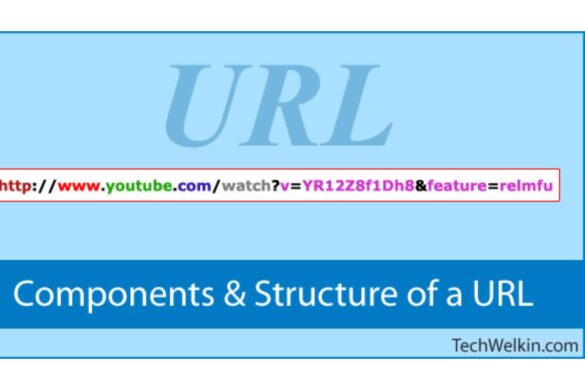
URLs
URLs help provide a way to access information on the Internet from a computer, for example, cloud storage or a…